SerpScan -Automate your Recon using search engines
Serpscan is a powerful PHP tool designed to allow you to leverage the power of dorking straight from the comfort of your command line.
As in the title, today I’m presenting a new tool, but maybe it’s an idea more than a tool for those who are looking to make an automated vulnerabilities scanner for bug hunting, and for those companies who have plans to make a paid pen-testing services.
You’re a bug bounty hunter? — I’m not sure if you’re familiar with this information or no, but the top security companies and some of the TOP 100 hackers on the HackerOne platform are using automated tools that gathering information, Dorking, checking for CVE’s and making ready to go reports for them.
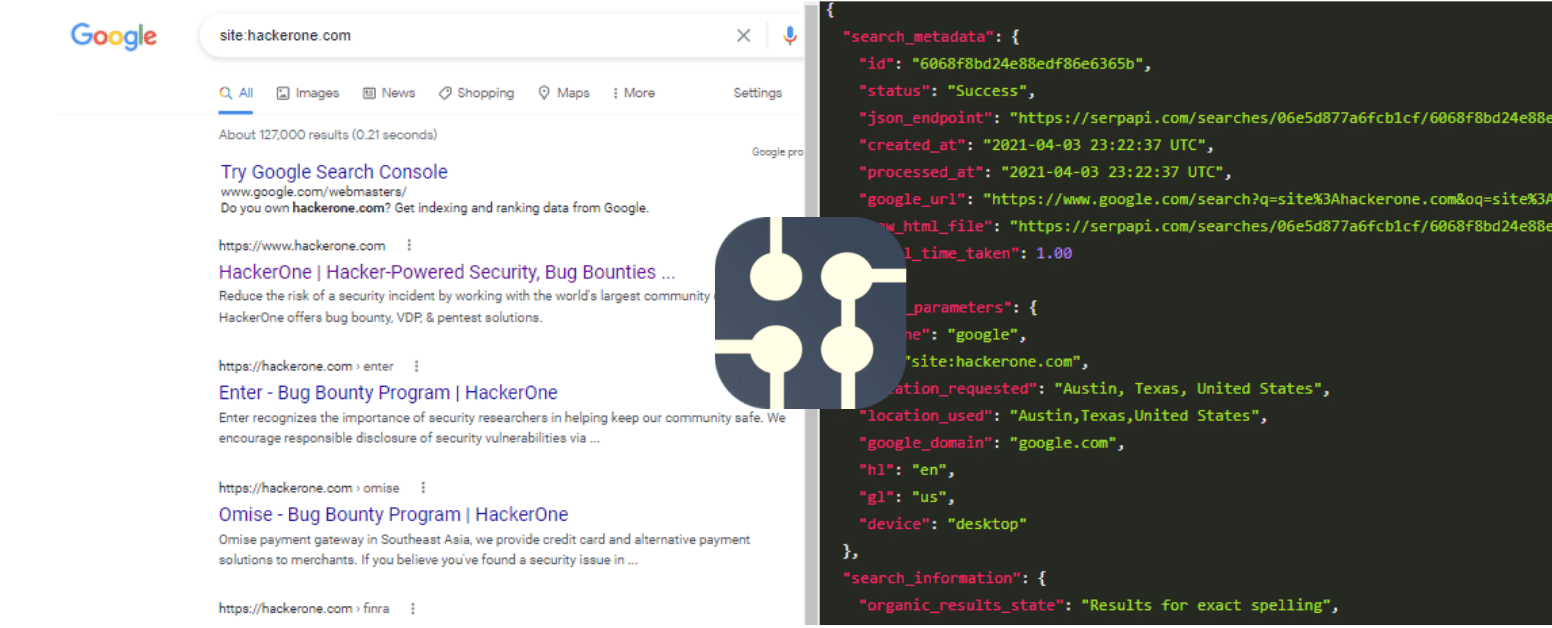
There are already a lot of scanners with built-in API that can be used, but these scanners cannot provide such a service which is SerpApi.
The idea here, you’re not going to check every dork manually one by one of course, so here it comes the SerpApi and SerpScan tool…
SerpApi is a service that gives you an API for the known search engines, such as Google, Bing, etc.
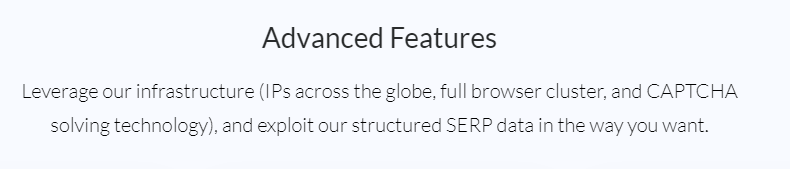
And the searches in Real-time, their API is based on different IPs, CAPTCHA solving technology, and more…
So What is SerpScan? —it is a powerful PHP script designed to allow you to leverage the power of Dorking straight from the comfort of your command line, You just have to enter your target, the tool automatically will gather the information about your target from all search engine pages.
Features
- Scan multiple domains.
- Subdomain Enumeration.
- Checks the alive subdomain.
- Finds URLs from all search engines.
- Finds js files.
- Search endpoints in js files.
- Finds parameters.
- Finds directories.
- Export results in HTML,JSON.
- You can customize your dorks in the config file.
Right now there are already basic Dorks in the config.php file, and you could add as much as you want.
<?php
require __DIR__ . '/vendor/autoload.php';
require __DIR__ . '/SAPI.class.php';
ini_set('max_execution_time', 0);
set_time_limit(0);
date_default_timezone_set('Asia/Riyadh');
// Replace with your API key.
$APIKey = 'a89ab7d75ddaab3c0ece0a1253ee64751148adbe221b1b35863879d8f09edeec';
$outputPath = 'result';
$usePackage = true;
$domainsFile = 'domains.txt';
// query need to search , {{DOMAIN}} not change ever
$engine = [
['google', 'q', [
'subDomain' => 'site:.{{DOMAIN}}', // not change key
'SQLErrors' => 'site:{{DOMAIN}} intext:"sql syntax near" | intext:"syntax error has occurred" | intext:"incorrect syntax near" | intext:"unexpected end of SQL command" | intext:"Warning: mysql_connect()" | intext:"Warning: mysql_query()" | intext:"Warning: pg_connect()"',
'PubDocum' => 'site:{{DOMAIN}} ext:doc | ext:docx | ext:odt | ext:rtf | ext:sxw | ext:psw | ext:ppt | ext:pptx | ext:pps | ext:csv',
'PHP_Err_Warn' => 'site:{{DOMAIN}} "PHP Parse error" | "PHP Warning" | "PHP Error"',
'PHP_INFO' => 'site:{{DOMAIN}} ext:php intitle:phpinfo "published by the PHP Group"',
'DirLIstVuln' => 'site:{{DOMAIN}} intitle:index.of',
'ConfigsFiles' => 'site:{{DOMAIN}} ext:xml | ext:conf | ext:cnf | ext:reg | ext:inf | ext:rdp | ext:cfg | ext:txt | ext:ora | ext:ini | ext:env',
'PastingSites' => 'site:pastebin.com | site:paste2.org | site:pastehtml.com | site:slexy.org | site:snipplr.com | site:snipt.net | site:textsnip.com | site:bitpaste.app | site:justpaste.it | site:heypasteit.com | site:hastebin.com | site:dpaste.org | site:dpaste.com | site:codepad.org | site:jsitor.com | site:codepen.io | site:jsfiddle.net | site:dotnetfiddle.net | site:phpfiddle.org | site:ide.geeksforgeeks.org | site:repl.it | site:ideone.com | site:paste.debian.net | site:paste.org | site:paste.org.ru | site:codebeautify.org | site:codeshare.io | site:trello.com "{{DOMAIN}}"',
'DBFiles' => 'site:{{DOMAIN}} ext:sql | ext:dbf | ext:mdb',
'SearchGit' => 'site:github.com | site:gitlab.com "{{DOMAIN}}"',
'SearchStack' => 'site:stackoverflow.com "{{DOMAIN}}"',
'LogsFiles' => 'site:{{DOMAIN}} ext:log',
'BackupFiles' => 'site:{{DOMAIN}} ext:bkf | ext:bkp | ext:bak | ext:old | ext:backup',
'LoginPages' => 'site:{{DOMAIN}} inurl:login | inurl:signin | intitle:Login | intitle:"sign in" | inurl:auth',
'SignupPages' => 'site:{{DOMAIN}} inurl:signup | inurl:register | intitle:Signup',
]],
['baidu', 'q', [
'subDomain' => 'site:.{{DOMAIN}}', // not change key
]],
['bing', 'q', [
'subDomain' => 'site:.{{DOMAIN}}', // not change key
]],
['yahoo', 'p', [
'subDomain' => 'site:.{{DOMAIN}}', // not change key
]],
['yandex', 'text', [
'subDomain' => 'site:{{DOMAIN}}', // not change key
]]
];The current dorks will check for :
Publicly exposed documents Directory listing vulnerabilities Configuration files exposed Database files exposed Log files exposed Backup and old files Login pages SQL errors PHP errors / warnings phpinfo() Search Pastebin.com / pasting sites Search Github.com and Gitlab.com Search Stackoverflow.com Signup pages
Installation
First, you need to download or clone the Github repo for this tool here
- git clone https://github.com/Alaa-abdulridha/SerpScan.git
- cd SerpScan
- chmod +x install.sh
- ./install.sh
The install.sh file here will support two systems only:
Ubuntu(Tested on 18 and 20) and CentOS 7.
It could be easily installed manually, I tested it on windows as well, there’s a Docker image provided with the tool.
To use Docker all you have to do is :
docker run -it alaa0x2/serpscan:latest php
/usr/src/SerpScan/start.php -d domain.com -t htmlHowever don’t forget to put your API key in config.php, You can grab your API key from https://serpapi.com
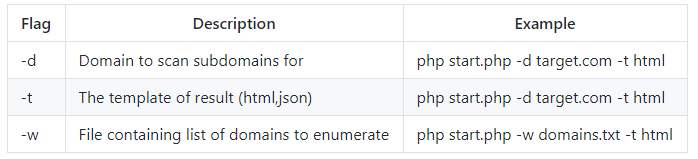
Usage
the Argument of -t must be used in all cases, you could enter multiple targets in the domains.txt file.
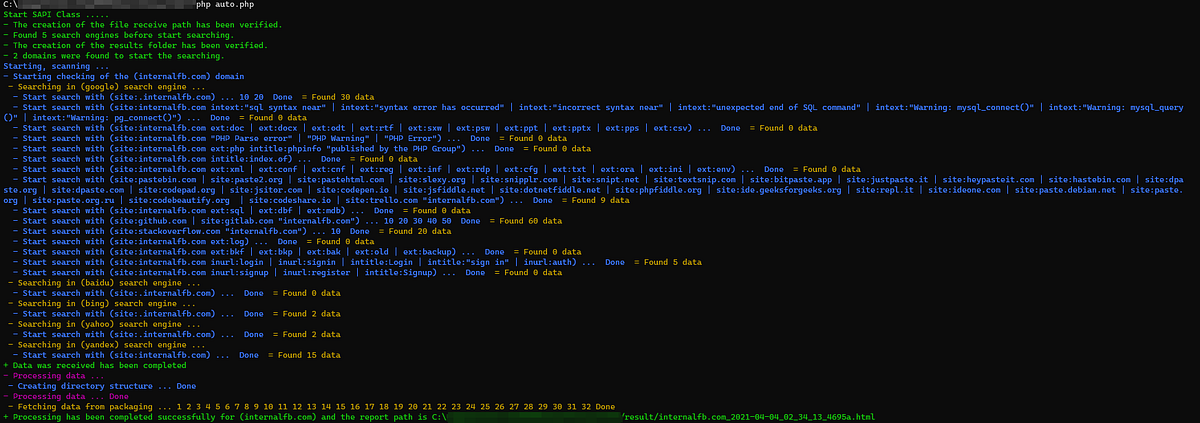
I will leave you with the results 🙂

This tool is just an example of what you could achieve by using SerpApi to automate your bug hunting 😀
Check the GitHub repo, there’s a sample of the report that is provided.
And as I mentioned before you could grab your API Key from https://serpapi.com
it’s the cheapest website out there and the best to provide you with this service with a great team, and they will provide you with a free 5000 search credits or more (Which it’s really a lot).
Cheers.